Attackers don’t start with your homepage—they start with your system paths, hidden files, and known weak points.
Your access logs, CSF/LFD logs, and honeypot traps reveal the same pattern over and over again:
Hackers and scanners hit the same 12 URLs first when probing a WordPress site.
These early probes tell you exactly what type of attack is coming next.
Below are the most-abused WordPress URLs in 2026, what each request means, and how to detect and block the attackers before they touch your WordPress install.
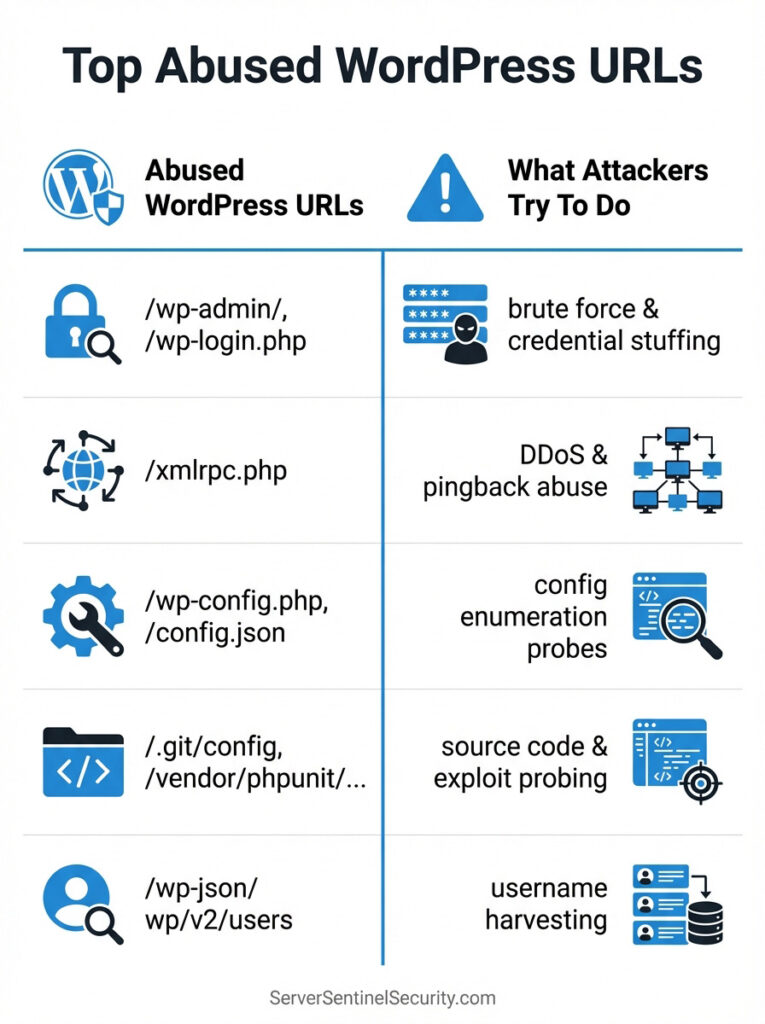
1. /wp-login.php — Automated Credential Stuffing
Why attackers target it:
It’s the primary login page. Bots attempt:
- password spraying
- credential stuffing
- username enumeration
- XML-RPC assisted brute-force (if enabled)
Detection:
- Sudden POST requests to
/wp-login.php - A large number of 200 or 403 responses from foreign IPs
- Unusual user-agents (
Mozilla/5.0 (l9scan...), fake browsers, headless clients)
Best defense:
- Limit attempts at the server firewall
- Block known bot ASNs
- Add a honeypot fake-login endpoint
2. /xmlrpc.php — Attack Gateway
Why attackers hit it:
XML-RPC allows hundreds of login attempts in a single request.
Also used for:
- DDoS amplification
- Pingback exploitation
- Authentication bypass scanning
Detection:
Look for:
POST /xmlrpc.php 200
User-Agent: Python
Best defense:
- Disable it at the server
- Or serve a honeypot version that automatically blocks offenders
3. /wp-admin/ — Admin Console Recon
Attackers check this to:
- confirm WordPress version
- probe admin-ajax or admin-post
- map your backend paths
Detection:
500 or 403 hits to /wp-admin/ from foreign IPs.
Defense:
- Restrict to your IP
- Block automated scanners
- Add rate limits
4. /wp-admin/admin-ajax.php — Vulnerable Plugin Endpoint
Used by thousands of plugins. Botnets abuse it to find:
- outdated plugin versions
- file upload vulnerabilities
- information leaks
Detection:
Unusual POST requests with empty parameters.
Defense:
Honeypot the endpoint for non-logged-in users.
5. /wp-json/ — REST API Scanning
A treasure map for attackers.
It reveals:
- usernames
- plugin endpoints
- theme data
- routes that may be vulnerable
Detection:
High-frequency GET requests from a single IP.
Defense:
Restrict anonymous access.
Rate-limit at the firewall.
6. /.git/config — Source Code Theft Attempt
This is a top hit you see in your own logs.
Bots check this to download your entire repo.
Detection:
Any request to /.git/ is malicious.
Defense:
Immediate block via CSF or ipset.
7. /vendor/phpunit/phpunit/phpunit — PHPUnit RCE Exploitation
Old plugin folders sometimes contain PHPUnit—which has a major RCE flaw.
Attackers check if it exists.
Detection:
Requests to any /vendor/ folder inside wp-content.
Defense:
Harden with file-level blocks.
8. /wp-content/plugins/*/readme.txt — Version Enumeration
Bots crawl your plugin folders trying to extract plugin version numbers.
Detection:
Multiple 200 hits on plugin readmes.
Defense:
Block direct plugin folder listing.
9. /wp-content/uploads/* — Malicious File Upload Attempts
Attackers test:
- random file uploads
- known vulnerable upload endpoints
- direct file execution
Detection:
Odd extensions: .php, .phtml, .phar, .zip, .rar.
Defense:
Disable PHP execution in uploads.
10. /config.json — LeakIX Fingerprinting Probe
You are seeing this in your logs:
Mozilla/5.0 (l9scan/... +https://leakix.net)
LeakIX uses this to detect exposed config files.
Detection:
Any request for config.json or .env.
Defense:
Hardkill immediately + add their IP ranges to deny lists.
11. /wp-includes/ — Core File Enumeration
Scanners try to identify:
- WordPress version
- outdated core files
- exposed scripts
Detection:
Requests for JS/CSS files that no human would browse.
Defense:
Rate-limit and block suspicious user agents.
12. /robots.txt — Mapping Your Forbidden Pages
If your robots.txt hides admin areas, attackers use it as a hit list.
Detection:
Robots.txt is immediately followed by requests to blocked URLs.
Defense:
Keep robots.txt minimal.
How to Detect These Probes Early (Before WordPress Loads)
Attackers leave fingerprints long before they reach WordPress.
Here’s how to catch them early:
1. Analyze Raw Access Logs
When reviewing your raw access logs, look for patterns that indicate automated probing or early-stage attacks. These include repeated requests to the high-risk URLs listed earlier, bursts of rapid-fire hits from the same IP address, unusual or clearly fabricated user agents, and geographic anomalies such as login attempts from countries with no relationship to your site. Seeing any of these patterns means a scanner is already testing your perimeter.
2. Use a Real Honeypot
A properly designed honeypot gets triggered immediately because scanners follow highly predictable URL paths and attack sequences. Your honeypot will record standard probes like /.git/config, config.json, fake admin paths, fake plugin or theme endpoints, and traffic from known scanners such as LeakIX and L9scan. This gives you immaculate, intention-based data—far clearer than anything a WordPress plugin log can provide—because only malicious automation ever touches the honeypot.
3. Block at the Server Firewall (Not in WordPress)
Server-level firewalls like CSF/LFD allow you to take action before WordPress even loads. You can block individual IPs, entire ASNs, and known scanner networks; add deny rules for malicious URL patterns; track and auto-block abusive 404 behavior; detect brute-force and syntax-based attacks; and automatically ban scanners using fingerprints like l9scan or L9Fingerprint. WordPress plugins, by contrast, only see the request after it reaches PHP—meaning the attack is already “inside” your environment by the time they attempt to block it.
Final Thoughts
WordPress attackers don’t start with complicated payloads—they start by checking these 12 URLs.
If you detect them early, you can block the attacker before they ever load WordPress core, bypassing:
- plugin firewalls
- brute-force protection plugins
- rate limits
- Cloudflare challenges
Server-level protection is the only reliable defense in 2026.
For More Information
For deeper insight into how attackers exploit specific WordPress URLs and vulnerable plugin endpoints, you can reference the NIST National Vulnerability Database (NVD)—the primary federal resource that catalogs confirmed security vulnerabilities and common exploit vectors used by automated scanners.
Protect Your WordPress Site Before Hackers Find These URLs
If you’re seeing suspicious entries in your logs—or you want to harden your VPS before attackers scan it—Server Sentinel can help.
👉 Explore our Firewall + Honeypot Packages
👉 Request emergency support now